2025湾区杯部分pwn复现
boom
checksec
1 | |
IDA
开局是一个猜数字的小游戏,输入
1 | |
即可进入 heap 界面
heap
1 | |
add
1 | |
off-by-null
delete
1 | |
edit
1 | |
只有一次的 edit 机会
分析
需要构造 overlap 但是只存在 off-by-null,并且该漏洞只出现在 add 时,所以我们需要利用 delete 后分配而保存下来的指针构造 unlink
步骤:
- 首先分配一些堆块
1 | |
- 在利用 C0 伪造指向 A D的两个指针和 size=0x551
1 | |
接下去就需要伪造 A->bk 和 D->fd
- 伪造 A->bk
1 | |
这一个块刚好也可以用来泄露 heapbase
- 伪造 D->fd
1 | |
- 最后伪造 pre_size 和 pre_inuse
通过 chunk5,来伪造并且unlink
1 | |
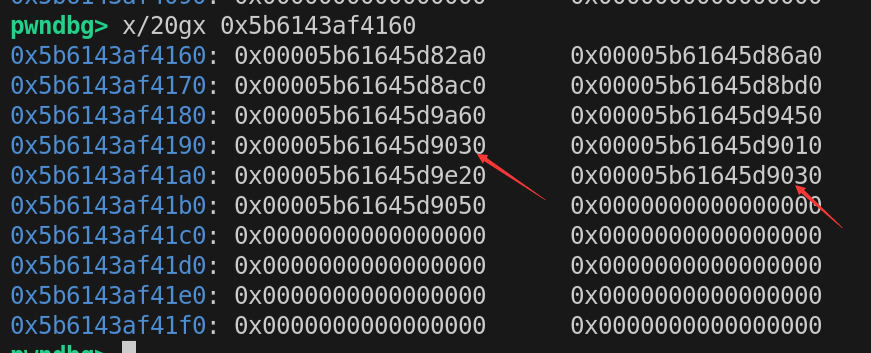
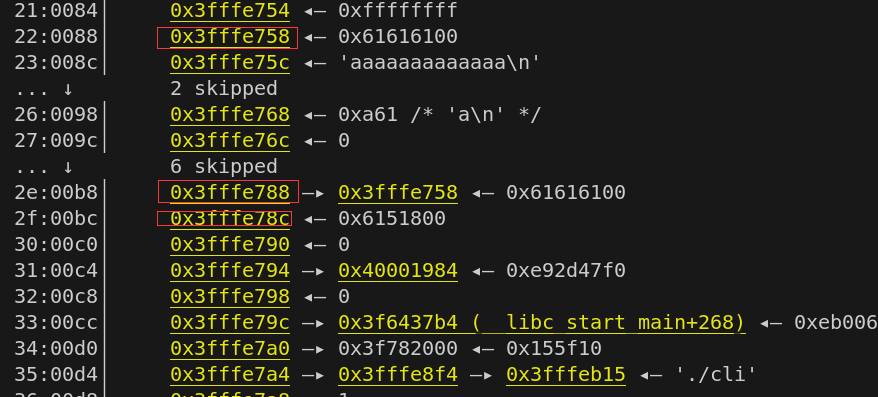
此时 chunk_list 和 bins 情况如下(bins中就是我们 overlap 得到的)
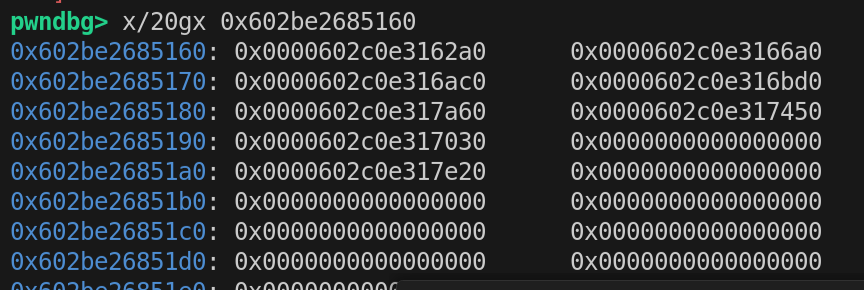
- 泄露 heapbase
1 | |
- 泄露 libcbase
1 | |
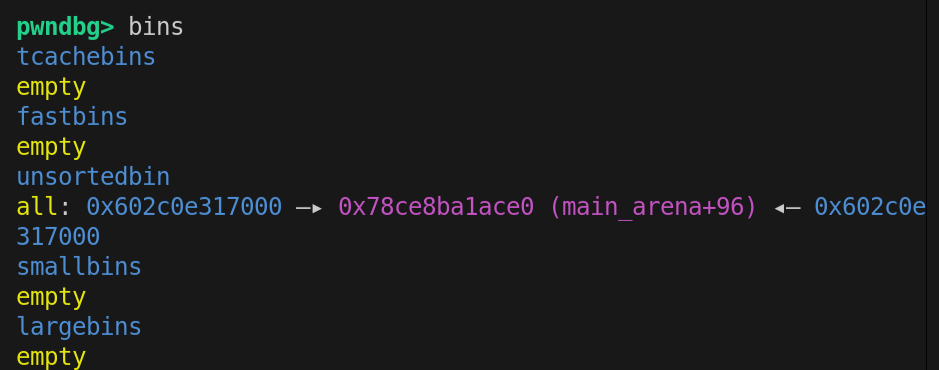
- puts 所调用的 libc 的 got 表地址
当我们调用puts的时候,会调用
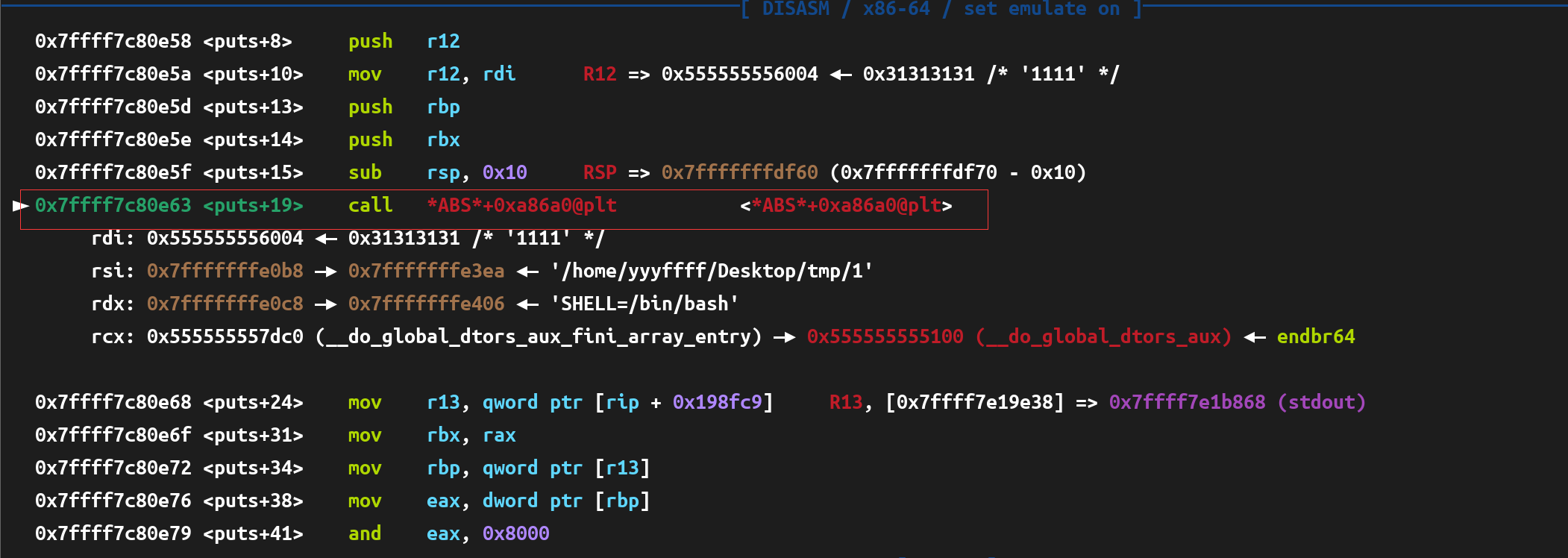
这句表示跳到某个表项(GOT),但该表项并不属于可执行文件的本地符号,所以用 *ABS* 表示一个绝对表项/外部表。
进入
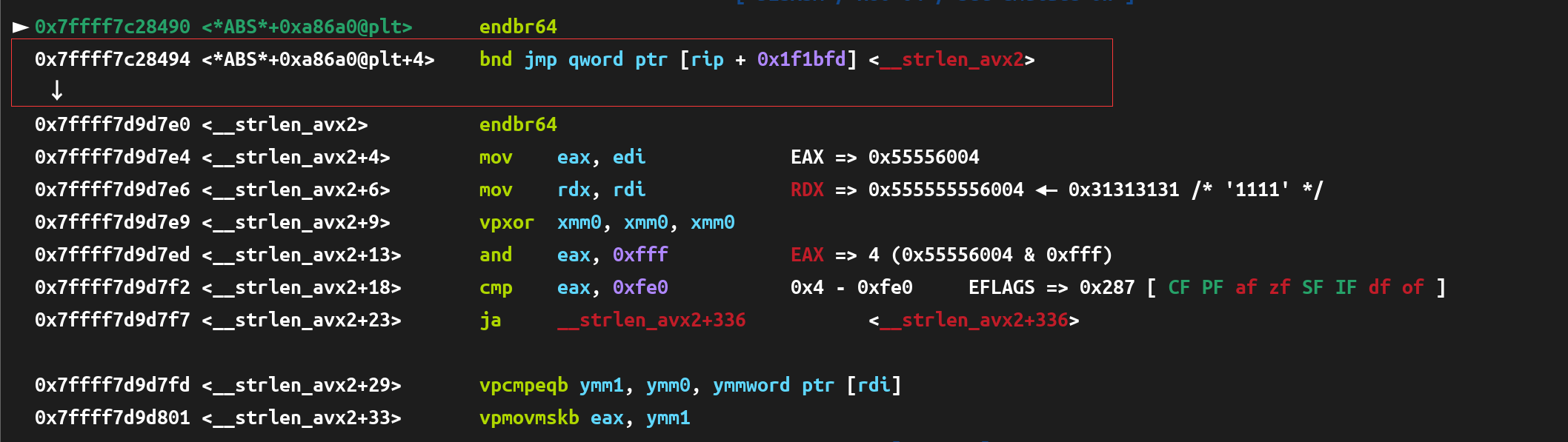
框起来的会 jmp 到一个地址,而该地址为 0x7ffff7c28494+7+0x1f1bfd
而该地址
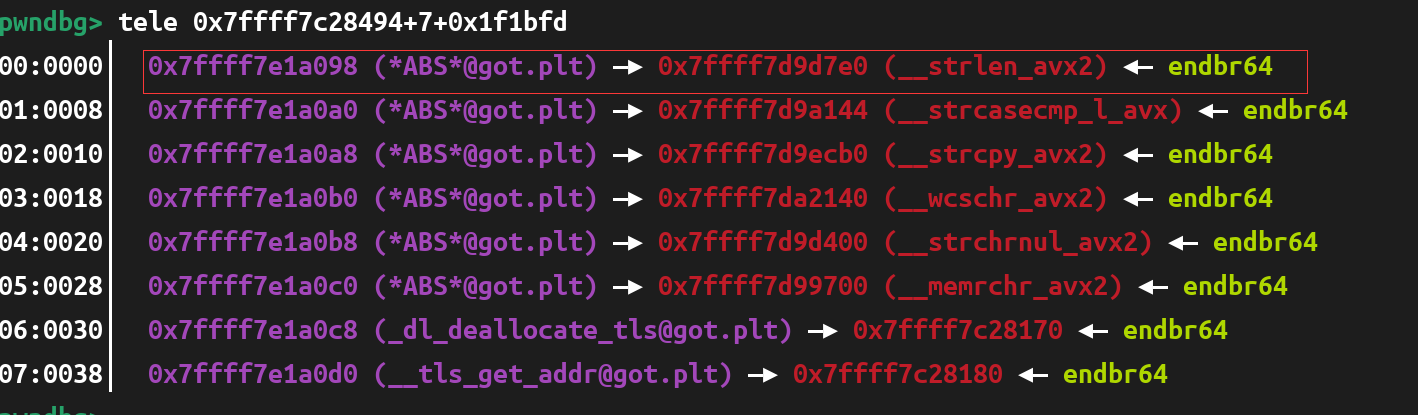
是一个属于 libc 的 got 表处,由于 libc 的 got 表是可写的,我们就可以修改该地址处为 ogg,以得到 shell
- 构造 tcache 来达到任意地址写
1 | |
exp
1 | |
signal
checksec
1 | |
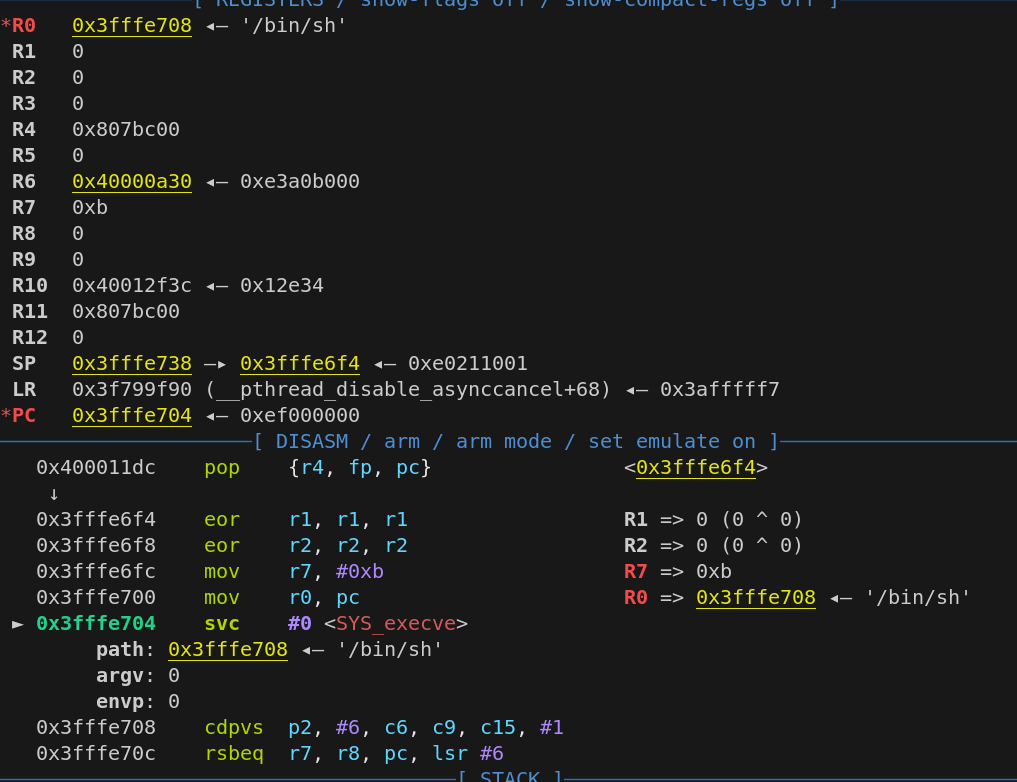
可以看到是arm架构32位程序
不过虽然开了 NX 但是栈依旧可执行
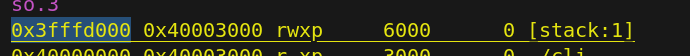
而后面有栈溢出,我们就可以做ret2shellcode
IDA
1 | |
sub_BAC
1 | |
sub_DF0(选项1)
1 | |
sub_101C(选项2)
1 | |
选项3和选项4都是没啥用的,不放伪代码了
分析
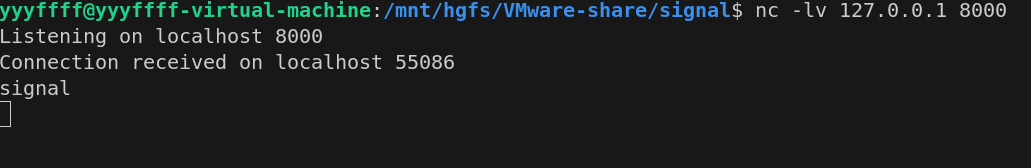
- 一些准备工作,需要开启监听 8000 端口后运行程序
1 | |
s 就是接收 signal 那个线程的,我们可以通过 s 来更改红绿灯信号
- 首先要控制 sig1=3,这里控制 sig1=3,sig2=5,然后需要确定偏移来泄露栈地址和 canary ,利用gdb-mutiarch 来调试程序
从 0089 开始输入,偏移分别为 0x2f 和0x33
所以
1 | |
- 进入选项2,填充上 canary 和 stack 地址,栈溢出 ret2shellcode
1 | |
效果如下
exp
1 | |
有个随机数的存在,所以有时候会不通,多运行几次就可以了
2025湾区杯部分pwn复现
http://yyyffff.github.io/2025/09/17/2025湾区杯部分pwn复现/